Trusted cybersecurity and IT expertise
Phoenix Cyber’s cybersecurity services are designed to enhance the overall security posture of your organization and protect it against cyber threats, attacks, and data loss. We assist organizations in identifying, assessing, and mitigating potential risks and vulnerabilities across your enterprise.
Our strategic and technical subject matter experts understand the importance of building operational processes and metrics while simultaneously designing and successfully deploying technically focused initiatives. This strategy ensures your security tools are quickly integrated into your security operations processes and immediately provide ROI.
Security Engineering and Architecture
Implementing a new tool into your existing processes can be challenging. Our security engineers have vast experience planning, architecting, designing, and integrating leading enterprise security tools and applications tailored to fit your requirements in the most complex and highly regulated security environments.
Security Operations
Establishing and operationalizing a security operations center (SOC) requires a thorough understanding of cybersecurity best practices that can and should be applied—either manually or automatically. Our cyber security experts are experienced in designing SOC infrastructures, defining threat monitoring and incident response processes, setting up security monitoring and log analysis, and creating playbooks and automated workflows tailored specifically to your security environment.
Technical Cybersecurity and IT Expertise
Maintenance activities are imperative to fostering and maintaining an effective security presence. We offer technical expert cybersecurity services that include standard maintenance, platform management, health checks, and technical support services to keep your security tools optimized. In most organizations, this administrative role is played by a separate engineering team that may not have the depth of knowledge needed to leverage the tools most effectively. We offer technical services as part of a holistic cybersecurity services engagement.
Cybersecurity domain expertise
Security technology advisory services and solutions
If you need help with a security tool that you already own, we can install, integrate, optimize, manage, automate, or build security operations playbooks to maximize the ROI for that product. If you need help choosing a security tool, we will assess your environment and recommend solutions that best fit your requirements. We have deep expertise in the following types of security tools and platforms:
Other Cybersecurity Services Resources
Frequently asked questions, answered
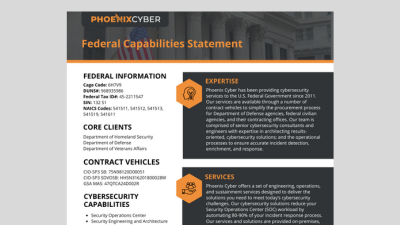
Phoenix Cyber helps federal organizations and enterprises enhance their security posture through comprehensive cybersecurity services spanning security AI and automation, engineering, operations, and strategic advisory. Our solutions ensure robust protection across complex IT environments, from initial assessment and tool selection through deployment, integration, optimization, and ongoing management.
Explore the most common questions we hear from security leaders evaluating cybersecurity services.
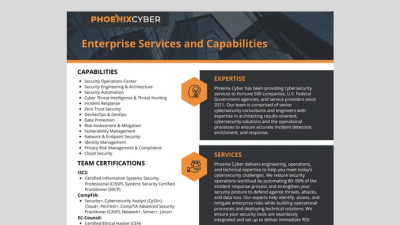
Phoenix Cyber delivers comprehensive cybersecurity services including security AI and automation, engineering and architecture, security operations, security orchestration, cloud security, data protection, zero trust implementation, DevSecOps, threat hunting, and vulnerability management, among other cybersecurity and technology disciplines. Our services are designed for both federal government agencies and enterprise organizations, with deep expertise in highly regulated environments. We provide end-to-end support from assessment and design through deployment, integration, optimization, and ongoing management and sustainment of security tools and platforms.
Phoenix Cyber specializes in designing, building, and operationalizing security operations centers tailored specifically to your environment and tooling. Our SOC services include infrastructure planning and architecture, threat monitoring and incident response process development, security monitoring and log analysis setup using SIEM platforms, playbook creation and automated workflow development, and the integration of multiple security tools (EDR, XDR, SOAR, TIP, DLP, etc.). We ensure your SOC aligns with cybersecurity best practices and compliance requirements while maximizing the ROI of your investments through automation and AI.
Yes, Phoenix Cyber is an established federal government contractor with over a decade of experience serving some of the largest U.S. federal agencies. We hold multiple contract vehicles including GSA MAS (HACS), GSA OASIS+, CIO-SP3, DLA JETS 2.0, and SeaPort NxG. Our cybersecurity services comply with federal regulations, frameworks like NIST and FedRAMP, and agency-specific security requirements. We specialize in implementing security solutions within highly regulated government environments and maintain ISO 9001:2015, ISO 27001:2013, ISO 20000-1:2011, and CMMI Level 3 certifications.
SOC automation and AI are complementary capabilities that together modernize how a SOC detects and responds to threats. Automation, typically delivered through SOAR platforms, executes predefined rule-based playbooks in response to specific triggers, handling high-volume repetitive tasks with speed and consistency. AI and machine learning go further by analyzing patterns across large data sets to surface anomalies, correlate subtle signals, and prioritize alerts that rules alone would miss. The most effective modern SOCs use both: AI to detect and prioritize, and automation to respond quickly and consistently. Phoenix Cyber has deep expertise in both areas, designing and implementing solutions with custom playbooks, orchestration workflows, and AI-driven capabilities that process and understand vast amounts of security data, reduce alert fatigue, lower MTTR, and keep your team focused on what matters most.
Absolutely, and this is something our team excels at. Phoenix Cyber helps to maximize the ROI of your existing security investments with services that include platform management and optimization, health checks and performance assessments, custom integration with other security tools, playbook and automation development, ongoing technical support and maintenance, and advanced use case development. Whether you have SIEM, SOAR, EDR, DLP, CASB, or other security platforms or AI tools, our security engineers and architects can enhance their effectiveness, automate processes, and ensure they’re properly integrated into your security environments to maximize efficiency and effectiveness of both the tool and your people.
Zero Trust is a security framework that eliminates implicit trust by continuously verifying every user, device, and network connection attempting to access resources regardless of location. At its foundation, the Zero Trust model specifically calls out automation as a core pillar, meaning it must be designed and baked in from the start, not bolted on later.
Phoenix Cyber implements Zero Trust through identity and access management (IAM) solutions, micro-segmentation and network access controls, continuous authentication and authorization, Zero Trust Network Access (ZTNA) deployment, integration of security analytics and monitoring, and adaptive security controls based on risk. Central to our approach is a robust orchestration and automation platform that operationalizes Zero Trust at scale, enabling consistent policy enforcement, rapid threat response, and seamless integration across your security ecosystem, all while maintaining compliance with federal and industry regulations.
Phoenix Cyber has deep technical expertise across leading enterprise security technologies including SIEM solutions (Splunk, Google SecOps, Securonix, Microsoft Sentinel), SOAR platforms (Swimlane Turbine, Palo Alto Cortex XSOAR, Splunk SOAR, Tines), EDR/XDR tools (CrowdStrike Falcon, SentinelOne Singularity, Microsoft Defender, Sophos Endpoint), DLP solutions (Forcepoint DLP, Symantec, Trellix, Proofpoint, Microsoft Purview), cloud security (Palo Alto Networks Prisma Cloud, CrowdStrike, Check Point, Fortinet, Zscaler), CSPM/CWPP platforms (Wiz, SentinelOne, Crowdstrike, Orca Security), IAM platforms (Okta, Ping Identity, Microsoft Entra, IBM Verify, Transmit Security), and vulnerability management tools (Tenable, Qualys VMDR, Rapid7 InsightVM, Arctic Wolf). We provide vendor-neutral advisory services to help you select the right security tools, then handle installation, integration, automation, and optimization.
Yes, Phoenix Cyber offers comprehensive DevSecOps services that embed security throughout the software development lifecycle. Our DevSecOps capabilities include designing and implementing secure CI/CD pipelines, integrating automated security testing (SAST, DAST, SCA), container security and Kubernetes hardening, infrastructure as code (IaC) security scanning, security automation and compliance integration, and collaboration process development across development, security, and operations teams. We help organizations accelerate secure software delivery while maintaining compliance with federal and industry security standards.
Deployment timelines vary based on project scope, complexity, and your environment, but Phoenix Cyber emphasizes agile methodologies to deliver value quickly. Our phased approach to deploying cybersecurity solutions typically includes initial assessment and planning, tool selection and procurement support (as needed), design and architecture, implementation and integration, testing and optimization, and knowledge transfer and training. For federal projects, we account for compliance requirements and security clearances. We can also provide longer-term operations and sustainment services as needed when a customer may need such services.
Yes, while cybersecurity is our core focus, Phoenix Cyber also provides complementary IT services and technologies to support secure operations. Our capabilities extend to application modernization programs, IT infrastructure services, cloud migration and modernization, application development and integration, IT service management and support, and project management for technology initiatives. These services are delivered with security best practices embedded throughout, ensuring that all technology implementations maintain robust security postures. Our holistic approach allows us to support organizations with end-to-end solutions that address both cybersecurity and broader IT needs, particularly valuable for federal agencies and enterprises requiring integrated technology services from a trusted, certified partner.