Resources
Implementing new cybersecurity processes and technologies requires research and due diligence. Our team has delivered cybersecurity services in some of the most demanding environment for over a decade. The resources on this page will help you better understand how utilizing various cyber security tools and strategies will benefit your security operations team.
Case Studies
Phoenix Cyber delivers groundbreaking privacy compliance application for Federal Government client
This case study details how Phoenix Cyber delivered a groundbreaking privacy compliance application for a Federal Government client that increased efficiency over 250% by automating privacy law and regulation compliance around personally identifiable information.
Phoenix Cyber delivers cybersecurity project management and security engineering expertise to Southwestern U.S.-based Integrated Health System
This case study describes how Phoenix Cyber provided cybersecurity project management and security engineering expertise to a Southwestern United States Integrated Health System throughout an ongoing 10-year relationship.
Datasheets
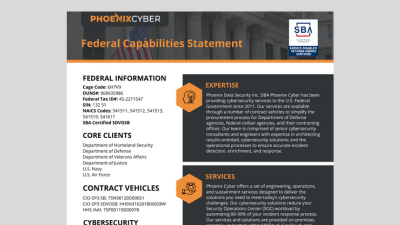
Federal Capabilities Statement
The Federal Capabilities Statement describes our expertise, capabilities, services, federal contract vehicles and past performance delivering cybersecurity services and solutions to U.S. Federal Government clients.
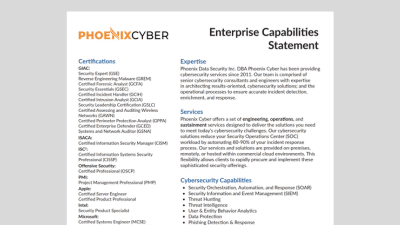
Enterprise Capabilities Statement
The Enterprise Capabilities Statement describes our expertise, capabilities, services, and industry certifications for delivering cybersecurity services and solutions to enterprise clients within the United States.
Privacy Compliance Management Solution Datasheet
This datasheet provides an overview of our solution for federal agencies that helps to ensure privacy compliance across the hundreds of information technology systems within your environment.
Videos
Next-Level Data Loss Prevention with Low-Code Security Automation
Watch this on-demand webinar replay to see how low-code security automation can help you streamline your DLP processes and reduce the risk of data loss.
Security Operations Center (SOC) Automation: Real World ROI
This 9-minute presentation shows how Security Orchestration, Automation and Response (SOAR) can reduce the time SOC analysts spend processing tickets—decreasing the organization’s Tier-1 workload by 75%.
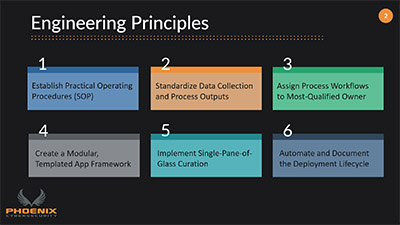
Security Orchestration, Automation and Response (SOAR) Engineering Principles
This 5-minute video will introduce you to the six security engineering principles that we follow when implementing Security Orchestration, Automation and Response (SOAR) solutions.